Original article: Windows 7 UAC – Quick notes on why I disable it. circa 2009
***31 December, 2020
As of today my original article is over eleven years old. Links to sources have disappeared. I updated the links today, mostly to the Internet Wayback Machine archive. I’ve also backed up these sources to PDF and have linked to those where appropriate.
Microsoft introduced User Account Control (UAC) with Windows Vista. Windows 7 has an “improved” version of UAC. The purpose of this short note is to explain why I do not like or use UAC on my own machines (because I get asked so much), it is not to start an argument or to try to convince others to disable UAC.
What is UAC?
UAC is designed to alert you before you do something that may have system wide implications. Installing a program or making system changes are among those things. When such an event occurs the user gets a prompt. The UAC prompt is there to say something like “Do you want the following program to make changes to your computer?”. What I see is something like, “Hey idiot, are you sure you know what you are doing?”.
UAC in Windows 7 is much improved over Vista. The annoying prompts are much less often. However as shown in the links below, UAC is not a security boundary. It isn’t for 3 reasons: The first is that it was never designed to be a security boundary, the second is that it can be bypassed, the third is that most users just click “Yes” (rendering it useless). In effect UAC draws a line in the sand and asks you if you want to cross it. Some would argue that UAC better than nothing but I’m not so sure. I am sure that UAC is not the barrier that many folks would have you believe. UAC is a line in the sand not a wall. It also cannot protect the ignorant and the lazy.
I’m not saying that UAC is useless for everyone or entirely bad. I install operating systems for many people and I would never disable it for someone else unless specifically requested to do so. I also ask if they were aware of the implications of disabling UAC. I reckon a line in the sand is better than nothing for some folks.
The links below contain the majority of material I have used to come to my conclusions on UAC.
(Yes I’ve read every word of every one of them. Yeah, I know, I’m a Geek.)
***Quick note 31 December, 2020
When I recommend or say disable UAC, this is to say disable the prompts. I have never and will never recommend disabling the UAC core.
You disable the prompts as I have stated in my tweak guides:
– Type or copy and paste UserAccountControlSettings.exe into the run box or Search box.
– In the resulting window, move the slider all the way to the bottom.
– Reboot
How User Account Control works (Microsoft) (PDF)
The slider will never turn UAC completely off. If you set it to Never notify, it will:
– Keep the UAC service running.
– Cause all elevation request initiated by administrators to be auto-approved without showing a UAC prompt.
– Automatically deny all elevation requests for standard users.
Readings on what UAC is:
Microsoft: What is User Account Control?
Inside Windows 7 User Account Control – Mark Russinovich
Windows 7: User Account Control (UAC) overview – Neowin
Microsoft: Windows 7 features – User Account Control
Microsoft: What’s New in User Account Control
Quotable Quotes
“UAC is a convenience feature; it neither introduces a security boundary nor prevents execution of malware.” Wikipedia (PDF)
“As we’ve stated since before the launch of Windows Vista, the primary purpose of elevation is not security, though, it’s convenience” Inside Windows 7 User Account Control – Mark Russinovich (PDF)
“It’s a best effort to raise the bar and stop malware from making changes to the operating system but it’s not a security boundary,” Mark Russinovich (PDF)
“Elevations are a convenience and not a security boundary,” Mark Russinovich (PDF)
“One important thing to know is that UAC is not a security boundary.” Engineering Windows 7 Blog (PDF)
“The reason we put UAC into the platform was to annoy users. I’m serious,” David Cross, Director of Program Management for Windows Security (microsoft) (PDF)
“we are seeing consumer administrators approving 89% of prompts in Vista and 91% in SP1.” Engineering Windows 7 Blog (PDF)
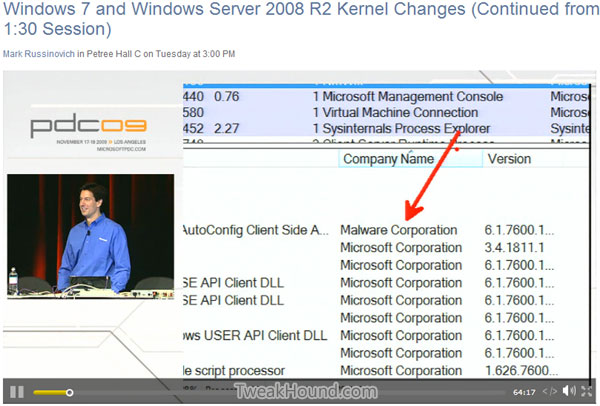
Mark Russinovich at PDC 2009 – Windows 7 and Windows Server 2008 R2 Kernel Changes
Link (DEAD): Windows 7 and Windows Server 2008 R2 Kernel Changes (Continued from 1:30 Session)
Video here: https://www.tweakhound.com/uac_pdfback/CL29.mp4
PowerPoint slides: https://www.tweakhound.com/uac_pdfback/CL04.pptx
“UAC does not stop you from malware”
“If Malware gets on your box and you are admain, you must assume that that malware will gain admin rights the second you ask for admin rights.”
“UAC is not about malware. It is about one thing and that is getting you guys to write your code so that it runs well as standard user.”
He actually demonstrates how approving a legitimate looking UAC prompt leads to a malware on the system.
Excellent third party articles on the shortcomings of UAC:
Within Windows – UAC, UAC, go away, come again some other day (PDF)
iStartedSomething – Sacrificing security for usability: UAC security flaw in Windows 7 beta (with proof of concept code) (PDF)
iStartedSomething – UAC in Windows 7 still broken, Microsoft won’t/can’t fix code-injection vulnerability (PDF)
iStartedSomething – Windows 7 UAC code-injection vulnerability: video demonstration, source code released (PDF)
ARS Technica – ARS Technica – Vista’s UAC security prompt was designed to annoy you (PDF)
ARS Technica – Windows 7 UAC flaws and how to fix them (PDF)
ARS Technica – Opinion: Windows 7’s UAC is a broken mess; mend it or end it (PDF)
TweakUAC – Am I at risk if I disable UAC? (PDF)
***You should know that when using Internet Explorer “If UAC is disabled, Protected Mode is turned OFF. When UAC is disabled, some of the protections which Protected Mode depends on are not available, for example, UI Privilege Isolation (UIPI) is disabled.” source IEBlog (PDF)
Final Thoughts
Whether or not you disable UAC is entirely your choice. This is simply my attempt at explaining why I disable UAC. I understand exactly what UAC is and isn’t. I have made an informed decision and weighed the consequences. I would encourage you to do some reading at the links above before you disable UAC. It should be noted that I have multiple images of all my systems and backups of data stored in multiple locations.
Want to argue about this subject or want to see what others have to say? Head over to The Great UAC Debate at Neowin
